Decentralization, n. The security presumption that a nineteen-year-old in Hangzhou and someone possibly located in the UK, who has yet to determine whether to collaborate with one another.
Recently, there has been considerable noise concerning the matter of mining centralization within the Bitcoin network. Observations were made of a single mining pool, GHash.io, accumulating over 45% of the hashpower for several hours and at one point even escalating to 51% of the total network. The Bitcoin subreddit’s main page ignited with fervent discussions and an uncommon clash of apathy and trepidation, leading miners to promptly shift their hashpower away from GHash. Ingenious strategies emerged in efforts to restore equilibrium among the various pools, including one miner with “between 50 TH/s and 2 PH/s” mining at GHash but refusing to submit valid blocks, effectively undermining all mining activities on the pool by as much as 4%. Currently, the situation has calmed somewhat, with GHash reduced to 35% network hashpower and the runner-up, Discus Fish, increasing to 16%. It’s probable that this circumstance will persist for at least a short duration before tensions escalate again. Is the dilemma resolved? Certainly not. Can this issue be resolved? That will be the central theme of this article.
Bitcoin Mining
To begin with, let’s grasp the issue at hand. The aim of Bitcoin mining is to establish a decentralized timestamping system, employing what is fundamentally a majority vote mechanism to determine the sequence of certain transactions as a solution to the double-spending dilemma. The double-spending issue is straightforward to elucidate: if I transmit a transaction sending my 100 BTC to you, and then one day later I execute a transaction sending the identical 100 BTC back to myself, both transactions cannot be processed simultaneously. Thus, one of the two must “prevail,” and intuitively, the transaction that deserves that recognition is the one that occurred first. However, there is no method to examine a transaction and cryptographically ascertain when it was created. This is where Bitcoin mining becomes essential.
Bitcoin mining operates by having nodes referred to as “miners” collect recent transactions and generate packages known as “blocks.” For a block to be legitimate, all transactions it includes must be valid, it must “reference” (i.e., include the hash of) a prior valid block, and it must fulfill “the proof of work condition” (specifically, SHA2562(block_header) 190, meaning that the double-hash of the block header must begin with a substantial number of zeroes). Since SHA256 is a pseudorandom function, the only means to produce such blocks is to continuously attempt to forge them until one fortuitously meets the requirement. The 2190 “target” is a flexible parameter; it adjusts automatically so that on average, the entire network needs to labor for ten minutes before one node succeeds. Once that occurs, the newly generated block becomes the “most recent” block, and every miner begins working on mining a block referencing that block as the prior block. This recurring process every ten minutes constitutes the central function of the Bitcoin network, generating an ever-growing chain of blocks (“blockchain”) that sequentially holds all transactions that have ever occurred.
If a node encounters two or more competing chains, it considers the longest one, i.e., the one with the most proof-of-work behind it, to be valid. Over time, if two or more chains are concurrently active, it becomes clear that the chain supported by greater computational power is likely to prevail; therefore, the system can be characterized as “one CPU cycle, one vote.” However, there is a vulnerability: if a single party or a colluding group holds over 50% of all network power, this entity alone gains majority control over the voting mechanism and can out-compute any other chain. This provides this party with some advantages:
- The party can only recognize blocks generated by itself as valid, thus obstructing any other miners because its own chain will consistently be the longest. Over time, this effectively doubles the miner’s BTC-denominated income at the detriment of all others. It is worth noting that a weaker variant of this attack, “selfish-mining“, begins to become effective at approximately 25% network power.
- The party can decline to include specific transactions (i.e., censorship)
- The party can “rewind” and commence mining from N blocks ago. When this fork inevitably surpasses the original, it eliminates the impact of any transactions that transpired in the original chain subsequent to the forking point. This can be utilized to gain illicit profits by (1) sending BTC to an exchange, (2) awaiting 6 blocks for the deposit’s confirmation, (3) purchasing and withdrawing LTC, (4) negating the deposit transaction and consequently transferring those coins back to the attacker.
This scenario describes the infamous “51% attack.” Importantly, however, even with 99% hashpower, the attacker does not acquire the ability to assign themselves an arbitrary quantity of new coins or to steal anyone else’s coins (apart from by reversing transactions). Another crucial point is that 51% of the network is not essential to initiate such attacks; if your sole objective is to defraud a merchant accepting transactions after a waiting period of N confirmations (usually,
N = 3or
```html
N = 6
), if your mining consortium owns a fraction P of the network, you can prevail with a likelihood of
(P / (1-P))^N; with 35% hashing power and 3 confirmations, this implies that GHash can presently pilfer altcoins from an altcoin exchange with a 15.6% chance of success – approximately once every six attempts.
Pools
This is where we discuss pools. Bitcoin mining is lucrative but, regrettably, a highly variable endeavor. If, in the present 100 PH/s network, you are operating an ASIC with 1 TH/s, then with each block, you have a probability of 1 in 100000 of acquiring the block reward of 25 BTC, yet on the other 99999 occasions out of 100000, you earn absolutely nothing. Considering that the network hash power is currently doubling every three months (for simplification, approximately 12500 blocks), this affords you a likelihood of 15.9% that your ASIC will ever produce a reward, and an 84.1% chance that the ASIC’s total lifetime revenue will be precisely zero.
A mining pool functions as a type of inverse insurance provider: the mining pool requires you to mine into its own wallet rather than yours, and if you generate a block whose proof of work is nearly sufficient but not entirely, termed a “share”, then the pool compensates you with a smaller amount. For instance, if the mining difficulty for the primary chain necessitates the hash to be less than 2190, then the criterion for a share could be 2190. Thus, in this scenario, you would produce a share roughly every hundred blocks, receiving 0.024 BTC from the pool, and one time in a thousand during those attempts, the mining pool will attain a reward of 25 BTC. The variance between the anticipated 0.00024 BTC and 0.00025 BTC per block represents the mining pool’s profit.
Moreover, mining pools fulfill an additional role. Currently, the majority of mining ASICs excel at hashing but are surprisingly deficient in other functionalities; the only component they generally possess for broader calculations is a diminutive Raspberry Pi, far too underpowered to download and confirm the complete blockchain. Miners could rectify this at the expense of something akin to an additional 0 is lower than $100. Instead, they request mining pools to produce mining data for them. The “mining data” in question pertains to the block header, a few hundred bytes of information that includes the hash of the preceding block, the root of a Merkle tree encompassing transactions, the timestamp, and additional supporting data. Miners utilize this information and continue to increment a value referred to as a “nonce” until the block header meets the proof-of-work criteria. Typically, miners would extract this data from the block that they independently identify as the latest block; nonetheless, in this instance, the actual determination of what constitutes the latest block is being delegated to the pools.
Consequently, what do we have? Currently, essentially this:
The mining ecosystem has consolidated into a relatively limited number of pools, with each holding a significant fraction of the network – and, certainly, last week one of those pools, GHash, achieved 51%. Given that whenever any mining pool, be it Deepbit in 2011 or GHash in 2013, attained 51% there was an abrupt, substantial drop in the number of users, it is entirely feasible that GHash genuinely has as much as 60% network hash power, and may be concealing some of it. There is considerable evidence in the real world of large enterprises fabricating allegedly competing brands to create an impression of choice and market vitality, so such a theory should not be dismissed. Even if GHash is indeed truthful about the extent of its hash power, this chart unequivocally indicates that the sole reason there are no 51% attacks obstructing Bitcoin at this moment is that Discus Fish, a mining pool managed by a nineteen-year-old in Hangzhou, China, and GHash, a mining pool purportedly operating in the UK but possibly situated anywhere, have not yet opted to collude with each other and dominate the blockchain. Alternatively, if one feels inclined to trust this particular nineteen-year-old in Hangzhou (after all, he appeared quite amiable when I met him), Eligius or BTCGuild might collaborate with GHash instead.
So, hypothetically speaking, what if GHash surpasses 51% again and initiates 51% attacks (or even begins targeting altcoin exchanges at 40%)? What are the consequences?
Firstly, let’s eliminate one flawed argument. Some contend that it does not matter if GHash exceeds 51%, as there’s no motivation for them to execute attacks against the network since even one such attack would obliterate the value of their own currency units and mining apparatus. Regrettably, this assertion is entirely ludicrous. To understand why, consider a hypothetical currency where the mining algorithm merely verifies signatures for my public key. Only I can authenticate blocks, and I have every motivation to uphold trust in the system. How could the Bitcoin community ignore my evidently superior, non-electricity-wasteful, proof of work? There are numerous responses: I could be irrational, I might be coerced by a government, I could gradually foster a culture where transaction reversals for certain “good purposes” (e.g., blocking child pornography payments) are deemed acceptable, and then eventually expand that to encompass all of my moral biases, or I might even have a substantial short position against Bitcoin at 10x leverage. Those two middle arguments aren’t fanciful hypotheticals; they are documented actions observed in the implementation of me-coin that already exists: PayPal. This highlights the importance of decentralization; we don’t waste millions of dollars on electricity yearly simply to transition to a currency whose ongoing stability relies on just a slightly different type of political maneuvering.
Moreover, it is critical to acknowledge that GHash itself has a track record of engaging in transaction reversal attacks against gambling websites; notably, one might recall the incident involving BetCoin Dice. Naturally, GHash refutes any intentional involvement, and likely rightly so; rather, the attacks appear to stem from a rogue employee. Still, this does not bolster GHash’s position; on the contrary, it serves as empirical evidence supporting a common argument favoring decentralization: power corrupts, and equally crucially, power attracts those who are already corrupt. In theory, GHash’s security has improved since then; in practice, irrespective of their actions, this central point of vulnerability within the Bitcoin network still persists.
However, a different and superior argument exists as to why mining pools are not problematic: specifically, the fact that they are not comprised of individual miners, but rather pools where miners can join and leave at their discretion. Because of this, one can justifiably state that Ars Technica’s assertion that Bitcoin’s security has been “shattered by an anonymous miner possessing 51% network power” is utterly erroneous; no single miner governs anything close to 51%. There is indeed a singular entity, known as CEX.io, that manages 25% of GHash, which is frightening itself but still falls far short of the situation the headline insinuates. If individual miners are unwilling to participate in undermining the Bitcoin protocol and inevitably diminishing the value of their coins by approximately 70%, they can simply exit the pool, which has already occurred three times in Bitcoin’s history. Nonetheless, the question remains: as the Bitcoin economy progresses towards professionalization, will this trend continue? Or, with somewhat more “greedy” individuals, will the miners persist in mining at the sole pool that allows them to continue generating revenue, individually preserving their profits at the expense of plunging the entire Bitcoin mining ecosystem into decline?
Solutions
Even now, there is indeed one tactic that miners can, and have, employed to undermine GHash.io: mining within the pool while intentionally withholding any valid blocks they discover. Such a tactic is untraceable, but with a 1 PH/s miner operating this way, it effectively diminishes the profits of all GHash miners by approximately 2.5%. This kind of pool sabotage entirely negates the advantage of utilizing the zero-fee GHash compared to other pools. The capability to penalize unethical actors is intriguing, although its implications remain ambiguous; what if GHash starts recruiting miners to conduct the same against every other pool? Thus, rather than depending on vigilant sabotage strategies with an unexamined economic outcome, we should ideally seek alternative solutions.
Firstly, there exists the ever-relevant P2P mining pool, P2Pool. P2Pool has been operational for years, functioning by maintaining its own internal blockchain with a 10-second block interval, enabling miners to submit shares as blocks within the chain and compelling miners to endeavor to generate blocks directed to all of the last few dozen share producers simultaneously. If P2Pool were to possess 90% network hashpower, the outcome
“`would not be centralization and a gracious dictatorship; instead, the extreme scenario would merely replicate the traditional Bitcoin blockchain. Nonetheless, P2Pool faces an issue: it necessitates miners to act as fully validating nodes. As noted previously, given the capability to mine without being a completely validating node, this is untenable.
One approach to this challenge, and the method that Ethereum is adopting, involves utilizing a mining algorithm that compels nodes to maintain the entire blockchain locally. A straightforward algorithm for this in the Bitcoin context is:
def mine(block_header, N, nonce): o = [] for i in range(20): o.append(sha256(block_header + nonce + i)) n = [] for i in range(20): B = (o[i] / 2**128) % N n.append(tx(B, o[i])) return sha256(block_header + str(n))
Where tx(B, k) represents a function that yields the kth transaction within block B, wrapping around modulo the total number of transactions in that block as necessary, and N denotes the current block index. It is worth noting that this represents a simplistic algorithm and is significantly suboptimal; some apparent enhancements involve making it serial (i.e., o[i+1] depends on n[i]), constructing a Merkle tree from the o[i] values to facilitate individual verification, and, as the Ethereum protocol presently does, sustaining a separate state tree and transaction ledger so that the algorithm only needs to reference the current block. A minor obstacle to effectively executing this in Ethereum is simply that the current trie mechanism lacks the notion of the “kth node” within a tree; the nearest parallel would likely need to be “the first node with a key lexicographically following k, with wraparound,” something that could feasibly produce a compact Patricia tree proof.
This effectively addresses two issues simultaneously. Firstly, it diminishes the motivation to opt for a centralized pool over P2Pool. Secondly, there exists a persistent dilemma in Bitcoin concerning the scarcity of full nodes; the underlying reason for this situation is that operating a full node with its 20GB blockchain entails significant costs, and few are willing to take it on. With this framework, every mining ASIC would be mandated to retain the entire blockchain, a condition from which executing all functions of a full node becomes straightforward.
An alternative strategy involves another cryptographic maneuver: rendering mining non-outsourcable. Specifically, the concept is to formulate a mining algorithm that ensures, when a miner generates a valid block, they invariably possess an alternative means of disseminating the block that secures the mining reward for themselves. The approach is to utilize a cryptographic structure known as a zero-knowledge proof, cryptographically certifying that they generated a valid block while keeping the block data confidential, and simultaneously creating a block devoid of proof of work that allocates the reward to the miner. This would simplify the process of defrauding a mining pool, rendering mining pools impracticable.
Such an arrangement would necessitate a substantial modification to Bitcoin’s mining algorithm, employing cryptographic components that are considerably more sophisticated than those present in the rest of Bitcoin; arguably,complexity presents a notable drawback on its own, one that may be worthwhile for addressing significant challenges like scalability but is not justified for executing a clever method to deter mining pools. Furthermore, rendering mining pools unviable could arguably exacerbate the issue rather than alleviate it. The existence of mining pools is primarily to mitigate variance; miners are reluctant to invest in an opportunity that offers only a 15% probability of generating any returns. Should pooling become impossible, the mining economy will inevitably centralize into a more confined group of larger entities – a scenario where, unlike the current state, individual miners would struggle to transition away. Meanwhile, the previous configuration still permits pooling as long as the local node possesses the complete blockchain, thus promoting a form of pooling (specifically, p2pool) that doesn’t pose systemic risks.
An alternative method is not as extreme: maintain the mining algorithm but modify the pooling algorithms. Presently, the majority of mining pools adopt a payout method known as “pay-per-last-N-shares” (PPLNS) – compensating miners per share based on the revenue from the last several thousand shares. This system effectively distributes the pool’s own variance among its members, leading to no risk for the pool and a minimal variance for the users (for instance, with a pool that holds 1% hashpower, the anticipated standard deviation of monthly returns is ~15%, which is a significant improvement over solo mining’s lottery-like risk but still not negligible). Larger pools experience less variance since they mine more blocks (based on basic statistical principles, a pool with four times the mining power possesses a half smaller standard deviation in percentage terms). There also exists a framework called PPS (pay-per-share), wherein a mining pool simply compensates miners a fixed amount per share; while this method eliminates all variance from miners, it introduces risk to the pool – hence, no mining pool employs it.
Meni Rosenfeld’s Multi-PPS seeks to offer a resolution. Rather than mining exclusively for a single pool, miners can work to generate blocks that reward multiple pools simultaneously (e.g., providing 5 BTC to one pool, 7 BTC to another, 11.5 BTC to a third, and 1.5 BTC to a fourth), with pools compensating the miner for shares in proportion (for instance, instead of a single pool paying 0.024 BTC per share, the first pool would provide 0.0048, the second 0.00672, the third 0.01104, and the fourth 0.00144). This setup enables very small pools to only cater to miners offering minimal rewards, thereby allowing them to take on risks corresponding to their economic capabilities. For example, if pool A is 10 times larger than pool B, then pool A might accept blocks with payouts of up to 10 BTC, while pool B might only accept 1 BTC. If one performs the calculations, it becomes apparent that pool B’s expected return is precisely ten times greater than what pool A receives under any circumstance, indicating that pool B has no extraordinary superlinear advantage. In a scenario employing single-PPS, however, the smaller pool B would encounter 3.16 times the risk relative to its wealth.
The question, however, is the extent to which this problem arises purely from variance, and to what degree it is attributed to other factors, such as convenience. Indeed, a mining pool with 1% share will experience a 15% monthly standard deviation in its earnings. Nevertheless, all mining pools generally encounter around a 40% monthly standard deviation in their returns simply due to the unpredictable BTC price fluctuations. The distinction between a 15% standard deviation and a 2% standard deviation appears significant, potentially providing a compelling reason to opt for the largest pool; the difference between 42% and 55%, however, seems less pressing. So, what other elements could contribute to mining pool centralization? One additional aspect is that pools inherently “hear” about their own blocks instantly, yet learn about others’ blocks following a certain network delay, meaning larger pools are less frequently mining on outdated blocks; this issue is critical for blockchains with a ten-second interval, but in Bitcoin, the impact is less than 1% and thus negligible. Another component is convenience; this can be optimally addressed by investing in an easy-to-use open-source solution to create your own mining pool, echoing the approach taken by many smaller VPS providers; should this be considered crucial, we might ultimately support a network-agnostic version of such an initiative. Yet, the last remaining factor is that GHash lacks any fees; instead, the pool maintains itself through its connection to the ASIC cloud-mining enterprise CEX.io, which commands 25% of its hashpower. Consequently, if we aim to thoroughly explore the centralization issue, it may require examining the ASICs themselves.
ASICs
Initially, Bitcoin mining was designed to be an extremely egalitarian endeavor. Millions of individuals worldwide would mine Bitcoin on their personal computers, leading to a distribution model that is highly equitable and significantly dispersing the initial BTC supply, alongside a consensus model that incorporates thousands of participants, effectively minimizing any chance of collusion. In its early days, this scheme functioned well, ensuring that the first few million bitcoins were widely distributed among numerous users, including those who were typically financially constrained high school students. However, in 2010, the emergence of mining software for GPU (“graphics processing unit”) took advantage of the GPU’s extensive parallel processing capabilities, achieving speedups of 10-100x and rendering CPU mining entirely unprofitable within a few months. By 2013, the trend of specialization escalated with the introduction of ASICs. ASICs, or application-specific integrated circuits, are specially designed mining chips created for a singular purpose: to execute as many SHA256 computations as possible for mining Bitcoin blocks. Due to this specialization, ASICs offer a further 10-100x speedup compared to GPUs, making GPU mining unviable as well. Thus, the sole available options for mining became establishing an ASIC business or acquiring an ASIC from an existing manufacturer.
The operational structure of ASIC companies is straightforward. Initially, the company is founded, conducts some foundational setup, devises its plan, and begins accepting preorders. These preorders subsequently fund the ASIC’s development, and once the devices are ready, they are dispatched to users, with the company commencing regular manufacturing and sales. The production of ASICs follows a pipeline model, involving one type of facility for chip manufacturing and another, less advanced, operation for assembling the chips with standard components like circuit boards and fans into completed units for shipping to buyers.
So, what does this mean for us? It is evident that ASIC production is considerably centralized; there are roughly 10-30 companies manufacturing these devices, each holding a notable portion of hashpower. However, I wasn’t fully aware of how centralized ASIC production really is until I visited an unremarkable building in Shenzhen, China:

On the third level of the factory, we observe:


The first image displays around 150 miners operating at 780 GH/s each, aggregating a total of 120 TH/s of mining power – representing over 0.1% of total network hashpower – all concentrated in one location. The second image reveals additional boxes containing another 150 TH/s. All told, thefactory generates slightly more than the total of these two figures – approximately 300 TH/s – each and every day. Now, take a look at this graph:
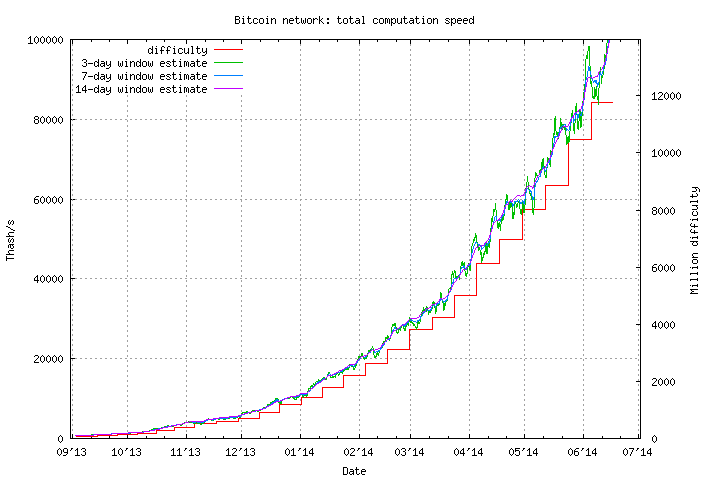
Overall, the Bitcoin network acquires around 800 TH/s daily. Therefore, even considering some margin for safety and presuming the factory is inactive on certain days of the week, we find one single factory responsible for producing more than a quarter of all newly generated hashpower being integrated into the Bitcoin network. Additionally, the facility is quite extensive, so can you guess what’s located on the ground floor? Correct, a manufacturing plant developing Scrypt ASICs that account for a quarter of all new hashpower added to the Litecoin network. This presents a daunting image for the future of Bitcoin: the Bitcoin network expending millions on electricity annually merely to replace the US dollar’s mining algorithm of “8 white individuals” with a few dozens of individuals in Shenzhen.
Nonetheless, before we become overly alarmist regarding the outlook of mining, it’s crucial to delve deeper and comprehend (1) what issues are associated with ASICs, (2) what advantages CPUs possess, and (3) how the future of ASIC mining is expected to evolve. The inquiry is more intricate than it appears. Initially, one could inquire, why is it problematic that ASICs are solely manufactured by a limited number of companies, with a quarter of them processed in one factory? CPUs are also significantly centralized; integrated circuits are produced by only a handful of firms, and almost all computers in use incorporate at least some components from AMD or Intel. The distinction is that, while AMD and Intel provide the CPUs, they don’t exert control over what’s executed on them. They are multipurpose devices, and there’s no mechanism for the manufacturers to translate their oversight of the production process into any form of dominion over its usage. DRM-influenced “trusted computing modules” are available, but it’s difficult to envision such technology being utilized to coerce a computer into partaking in a double-spend attack.
Presently, with ASIC miners, the situation is not too dire. Although ASICs are produced in only a limited number of facilities, they remain overseen by thousands of individuals globally across various data centers and residences, with individual miners, usually possessing less than a few terahashes, having the capacity to direct their hashpower as needed. However, this may soon alter. In a month’s time, what if the manufacturers recognize that it is not financially advantageous to market their ASICs when they could instead retain all their devices in a centralized warehouse and reap the entire revenue? Shipping expenses would diminish to nearly zero, shipping delays would decrease (a week of shipping lag equates to ~5.6% revenue loss at present hashpower expansion rates) and there would be no requirement to manufacture stable or aesthetically pleasing enclosures. In such a scenario, it wouldn’t only be 25% of all ASICs produced by one factory in Shenzhen; it would become 25% of all hashpower operating from a singular factory in Shenzhen.
During my visit to the headquarters of a firm in Hangzhou that engages in various activities, including Litecoin mining, I posed the founders the same question: why not retain the miners in-house? They offered three responses. Firstly, they are committed to decentralization. This concept is easily understood and it’s quite fortunate that many miners currently share this sentiment, but ultimately mining will be conducted by organizations that prioritize monetary gain over ideology. Secondly, they require pre-orders to finance the business. This is reasonable, yet could be addressed through the issuance of “mining contracts” (essentially, crypto-assets that provide dividends equivalent to a particular amount of GH/s of mining capacity). Thirdly, the available electricity and warehouse space are insufficient. The last point, as dubious as it may seem, could be the only one to have merit in the long term; it is also the publicly stated reason why ASICminer ceased exclusive in-house mining and began distributing USB miners to consumers, indicating that perhaps there is a compelling and widespread rationale behind such a choice.
Assuming that the funding methodologies of offering pre-orders and mining contracts are economically similar (which they are), the equation to evaluate whether in-house mining or selling is more viable is as follows:
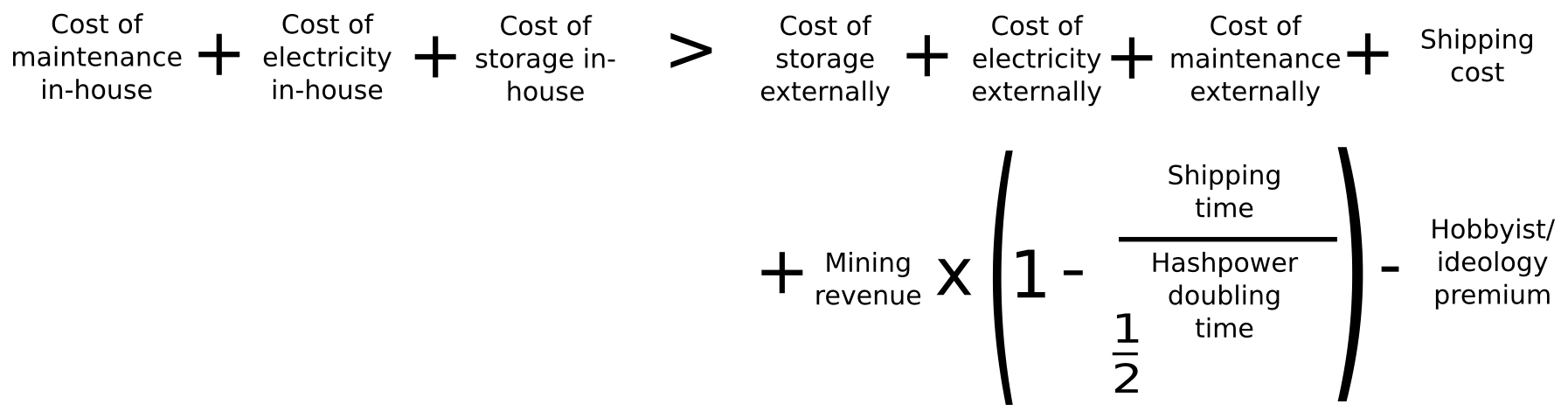
On the left side, we outline the expenses of in-house mining: electricity, storage and upkeep. On the right side, we detail the costs associated with electricity, storage and maintenance externally (i.e., in the possession of buyers), shipping fees, and the penalty incurred from delaying the operation of the ASIC, in addition to a negative factor to represent the reality that some individuals mine at least partially for enjoyment and from an ideological inclination to support the network. Let’s evaluate these calculations now. We’ll utilize the Butterfly Labs Monarch as our benchmark, operating each ASIC for a year for simplicity.
- Internal electricity, storage, maintenance – according to BFL’s checkout page, internal electricity, storage and maintenance incur a cost of $1512 annually, which we will estimate at $1000 assuming BFL retains some profit
- External electricity – in Ontario, the rates hover around $0.1 per KwH. A Butterfly Labs Monarch will perform at 600 GH/s at 350 W; normalizing this to a per-TH basis results in an electricity expense of $1.40 each day or $511 for the full year
- External storage – at home, one might consider storage to be free, or a convenience charge of $1 daily may be added; hence, we will estimate somewhere in the range from $0 to $365
- External maintenance – challenging to quantify this value; for technically adept individuals relishing the challenge, it’s effectively zero, while for others it may prove daunting; so we can approximate $0 to $730
- Shipping cost – per BFL, it’s $38.
- Revenue – currently, 1 TH/s yields 0.036 BTC or $21.6 daily. Given in our assessment hashpower doubles approximately every 90 days, leading to halving the efficacy of the ASIC every 90 days, we obtain 122 days of functioning or $2562 in revenue
- Shipping time – according to my contacts in China, one week
- Hashpower doubling time – three months. Thus, the complete expression for the shipping delay penalty is 2562 * (1 – 0.5 ^ 0.0769) = 133.02
- Hobbyist/ideology premium – presently, a significant fraction of Bitcoinminers are engaging in this activity due to ideological motives, which allows us to assert a range from $0 to $1000
Summing everything up, on the left we encounter $1000, while on the right we calculate $511 + $38 + $133 = $682, plus potentially $1095 and minus up to $1000. Therefore, it remains completely unclear which option is superior; miscalculations in my examination and the ambiguous factors regarding how individuals value their time and aesthetics seem to considerably overshadow any definitive outcomes. But what lies ahead? Essentially, one can anticipate that electricity, storage, and upkeep will be considerably less expensive on a centralized basis than for each individual user, purely due to economies of scale and specialization benefits; moreover, the majority of people in the “real world” are not altruists, enthusiasts, or fans of aesthetically pleasing ASIC casings. Shipping expenses are not negligible, and the penalties for shipping delays are significant. So it appears that the economics generally favor centralized mining…
… except for one possible element: heat. Presently, ASICs are still in a swift development stage, leading to the overwhelming majority of the expense being in hardware; the BFL miner referenced earlier costs 511. However, in the future, development will progress much more slowly; ultimately, we can foresee a convergence with Moore’s law, where hashpower doubles every two years, even as Moore’s law itself appears to be decelerating. In such a scenario, electricity expenses might re-emerge as the key limiting factor. But how much does electricity cost? In a centralized depot, quite a sum, and the square-cube law ensures that in a centralized context, considerably more energy will need to be devoted to cooling, since all miners are in one locality and most are too deep within the factory to benefit from fresh, cool air. In a household, however, if the external temperature is below approximately 20’C, the electricity cost could be null; all electricity consumed by the miner is eventually converted into “waste” heat, which then warms the home and substitutes for the electricity that would typically be used by a central heater. This serves as the sole argument for why decentralization of ASICs might be feasible: decentralization might occur not because individuals have a certain amount of unused, and thus free, computational time on their laptops, but because numerous individuals have a demand for heating in their residences.
Will this transpire? Many advocates of Bitcoin seem confident that the answer is affirmative. Nevertheless, I am uncertain; it is a completely empirical question whether electricity costs are less than maintenance plus storage plus shipping plus penalties for shipping delays, and in a decade, the equation could very well tip to one side or the other. Personally, I am not inclined to simply sit back and await favorable outcomes. This is why I find it disheartening that so many core Bitcoin developers (although fortunately not all) are content to consider the proof of work issue to be “resolved” or argue that efforts to tackle mining specialization constitute an act of “unnecessary re-engineering”. It might turn out to be the case, or it might not, but the mere fact that we are engaged in this discussion suggests that Bitcoin’s existing strategy is far from ideal.
ASIC Resistance
The most frequently recommended resolution to the ASIC dilemma is the creation of ASIC-resistant mining algorithms. Up to now, two primary lines of thinking have emerged in formulating such algorithms. The first is memory-hardness – diminishing the capacity of ASICs to achieve substantial advantages through parallel processing by utilizing a function that requires a considerable amount of memory. The community’s initial attempt was Scrypt, which proved inadequate resistance; in January, I sought to enhance Scrypt’s memory-hardness with Dagger, an algorithm that is memory-hard to compute (up to 128 MB) but easy to validate; however, this algorithm is susceptible to shared-memory attacks where numerous parallel processes may access the same 128 MB of memory. The current pinnacle of memory-hard PoW is Cuckoo, an algorithm that searches for length-42 cycles in graphs. Finding such cycles efficiently requires substantial memory, yet verifying a cycle is rapid, demanding only 42 hashes and less than 70 bytes of memory.
The second strategy varies somewhat: it involves establishing a method for producing new hash functions, generating a function space so vast that the most suitable type of computer for processing them is inherently completely generalized, i.e., a CPU. This approach comes close to being “provably ASIC resistant” and therefore more future-proof, rather than concentrating on specific characteristics like memory, but it too has shortcomings; there will always be parts of a CPU that will prove superfluous in such an algorithm and can be eliminated for efficiency. However, the objective is not to attain perfect ASIC resistance; rather, the challenge is to establish what we might refer to as “economic ASIC resistance” – making ASIC investments unjustifiable.
Remarkably, this may actually be feasible. To comprehend why, observe that the mining output per dollar spent is, for the majority, sublinear. The initial N units of mining capacity are remarkably inexpensive to generate since individuals can simply utilize their existing idle computational capacity on their desktops and only incur electricity costs (E). However, exceeding N units necessitates covering both hardware and electricity expenses (H + E). If ASICs are viable, provided that their speed advantage over standard hardware is less than (H + E) / E, then even within an ecosystem containing ASICs, it will remain profitable for individuals to allocate their electricity to mining on their desktops. This is the target we aspire to achieve; whether we can accomplish it remains entirely uncertain, but given that cryptocurrency as a whole represents a grand experiment, it does not hurt to pursue this objective.

